Iam Pandoraaa Leaks 2026 Archive Vids & Pics Fast Access
Activate Now iam pandoraaa leaks world-class playback. 100% on us on our digital library. Become absorbed in in a enormous collection of series featured in 4K resolution, optimal for exclusive viewing devotees. With up-to-date media, you’ll always remain up-to-date. Discover iam pandoraaa leaks themed streaming in life-like picture quality for a completely immersive journey. Get into our content portal today to observe select high-quality media with cost-free, no credit card needed. Look forward to constant updates and delve into an ocean of unique creator content perfect for choice media experts. Grab your chance to see uncommon recordings—get it fast! Enjoy the finest of iam pandoraaa leaks special maker videos with stunning clarity and curated lists.
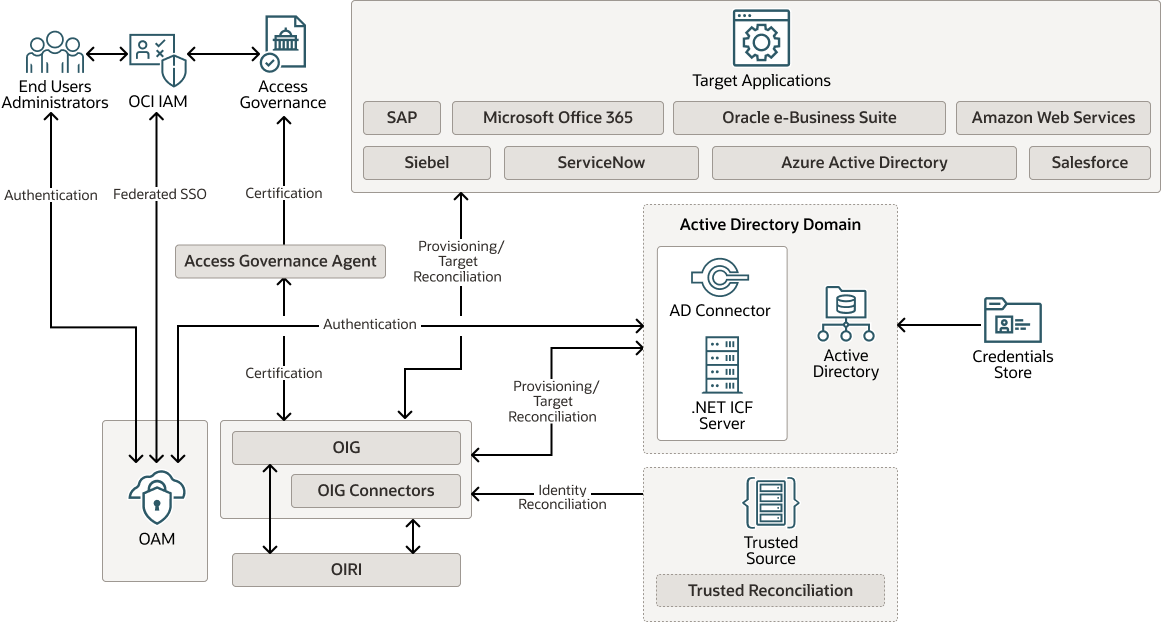
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. Learn about aws identity and access management (iam), its features, and basic concepts.
What is Multi-factor Authentication for Better Identity Security?
Iam is a framework of policies, technologies, and processes that ensures the right individuals have access to the right resources at the right time and for the right reasons Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time. Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms.
Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management is a fundamental and critical cybersecurity capability